Between 10:00 PM on Saturday December 16 and 4:00 AM on Sunday December 17 (Pacific time), approximately 25% of our hosting servers will be restarted. This will cause a brief interruption of service (less than 10 minutes) for those sites at some point during this 6 hour period.
You can follow the status of the maintenance on our system status page.
Read the rest of this entry »
Between 9:00 PM and 10:00 PM Pacific time on Monday, October 16, 2023, the MySQL database software on each of our servers will be upgraded from MariaDB version 10.5.19 to 10.5.21. This will cause an approximately 30-60 second interruption of service on each MySQL-using customer website at some point during this period.
For details, please see our status pages.
Between 10:00 PM and 11:59 PM Pacific time on Friday, September 29, each of our hosting servers will be restarted. This will cause a brief interruption of service (less than 5 minutes) for each site at some point during this 2 hour period.
You can follow the status of the maintenance on our system status page.
Read the rest of this entry »
We’ve traditionally used our blog for notifications about our system status, but we’ve now added a more modern status page, at www.tigertechstatus.net. It shows any problems, outages, or planned maintenance.
We recommend that you bookmark the page in your web browser so you can check it even if you can’t reach our main site for some reason. (It’s hosted by a third party, so it will be available even if there’s a problem with our services.) You can use the Get Updates button in the top of that page to subscribe to status updates by email, Slack, Microsoft Teams or RSS feeds.
Between 7:56 and 8:19 AM Pacific time today (August 26, 2022), a network outage at our data center caused most sites to be unavailable.
The underlying cause of the problem has been identified and resolved, and should not recur.
We apologize to our customers affected by this incident: we take reliability seriously, and don’t consider any outage normal or acceptable.
Between 5:18 PM and 5:41 PM Pacific time today, our “My Account” control panel was intermittently unavailable. This problem has been fixed and services are operating normally; we apologize for any inconvenience this caused.
If you’re seeing warnings in your web browser or mail program saying that an SSL certificate has expired (whether it’s for our tigertech.net site, for a site we host, or for millions of other sites completely unrelated to us, like dictionary.com), that’s happening because a “root” SSL certificate distributed as part of your computer operating system has expired.
This can happen if you’re using a computer or program that hasn’t been updated since 2016 (that’s when Microsoft, Apple and others started providing replacement certificates with their updates).
There are many pages online that talk about this in technical terms (here and here, for example), but the short answer to “how do I fix this” is to update your computer operating system if you can. That will fix everything.
If you can’t update your computer, you can use a recent version of the Mozilla Firefox web browser to avoid the problem when viewing websites. That works because Firefox includes its own updated root SSL certificates, instead of using the outdated ones that came with your computer and haven’t been updated.
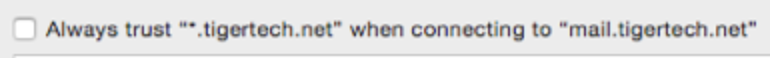
If you’re using an old version of a mail program that shows an error, it may allow you to add an “exception” or check a box telling it to always trust the certificate anyway — it might look like this if you show the certificate details, for example:
If it doesn’t allow that, you can either disable SSL in the settings of that mail program (for example, by unchecking the “Use SSL” checkbox in older versions of Apple Mail), or you can use the Firefox web browser to read your mail using webmail. If you’re one of our customers, that’s at webmail.tigertech.net.
Read the rest of this entry »
Over the next three weeks, we’ll be updating the MariaDB (MySQL) database server software on all our servers from the MariaDB 10.3 series to the MariaDB 10.5 series (equivalent to the Oracle MySQL 8.0 series).
The MariaDB/MySQL database stores pages for WordPress and other sites that are run by scripts. Customers should not notice any difference after this change; we’re upgrading it to a more recent version simply to make sure it’s as fast, reliable and secure as possible. We’ve been using the new version on internal and test servers for some time.
At the moment the software is updated on a server, WordPress and other database-backed sites on that server will have 30-60 seconds of unavoidable “downtime”. To minimize the impact of that, we do these upgrades only on Friday, Saturday and Sunday nights between 9 PM and midnight Pacific time (midnight-3 AM Eastern time). We expect this process to be complete on all servers by September 6.
Beyond that one-time brief interruption in service, customers should not notice any difference to how their site works, as we said. But as always, don’t hesitate to contact us if you have any trouble or questions.
Update 9:24 PM Pacific time September 5: This upgrade has been completed on all servers.
Between 10:00 PM and 11:59 PM Pacific time on Friday, July 16, each of our hosting servers will be restarted. This will cause a brief interruption of service (less than 5 minutes) for each site at some point during this 2 hour period.
Read the rest of this entry »
We’re upgrading our servers from Debian Linux version 9 (codename “stretch”) to version 10 (codename “buster”). We’ll be finishing that process over the next couple of weeks.
Your website and email should continue working as they always have, and we don’t expect any downtime. However, if you do have any trouble, don’t hesitate to contact us.
Although the final steps of the upgrade modify hundreds of software packages on the server, we’ve tested it extensively and don’t expect most customers to notice any change. (We’ve already been using the newer version of Debian for our own servers.)
Read the rest of this entry »