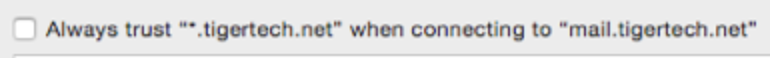
A company named “Domain Listings” is sending misleading “Annual Website Domain Listing” notices to domain name owners via postal (paper) mail. These notices are scams, in the sense that they’re designed to mislead you into thinking it’s an invoice or bill related to your domain name registration.
They look like this:
This ”Domain Listings” company has an “F” rating from the Better Business Bureau, with hundreds of complaints about this.
If you receive one of these letters from “Domain Listings”, don’t pay them (or any other company that sends you an unsolicited invoice for search engine services). You never need to pay for basic search engine listings. We have more tips on our page about this scam.
Today is World Backup Day! If you’re not backing up your own computer and devices, today’s the perfect day to start doing it; that page has advice.
Do you ever wonder how companies like ours handle backups? It’s a good question. Our customers trust us with lots of data — email, websites, and more. It’s important that we keep that data (and our own data) safe. We do that with a 4-3-2-1 backup policy:
- There are always at least 4 copies of the data;
- The data is stored on at least 3 different physical servers;
- The servers are in at least 2 separate physical locations;
- At least 1 copy of the data is always physically disconnected from power and the Internet (“air gapped”).
Read the rest of this entry »
We’ve traditionally used our blog for notifications about our system status, but we’ve now added a more modern status page, at www.tigertechstatus.net. It shows any problems, outages, or planned maintenance.
We recommend that you bookmark the page in your web browser so you can check it even if you can’t reach our main site for some reason. (It’s hosted by a third party, so it will be available even if there’s a problem with our services.) You can use the Get Updates button in the top of that page to subscribe to status updates by email, Slack, Microsoft Teams or RSS feeds.
If you’re seeing warnings in your web browser or mail program saying that an SSL certificate has expired (whether it’s for our tigertech.net site, for a site we host, or for millions of other sites completely unrelated to us, like dictionary.com), that’s happening because a “root” SSL certificate distributed as part of your computer operating system has expired.
This can happen if you’re using a computer or program that hasn’t been updated since 2016 (that’s when Microsoft, Apple and others started providing replacement certificates with their updates).
There are many pages online that talk about this in technical terms (here and here, for example), but the short answer to “how do I fix this” is to update your computer operating system if you can. That will fix everything.
If you can’t update your computer, you can use a recent version of the Mozilla Firefox web browser to avoid the problem when viewing websites. That works because Firefox includes its own updated root SSL certificates, instead of using the outdated ones that came with your computer and haven’t been updated.
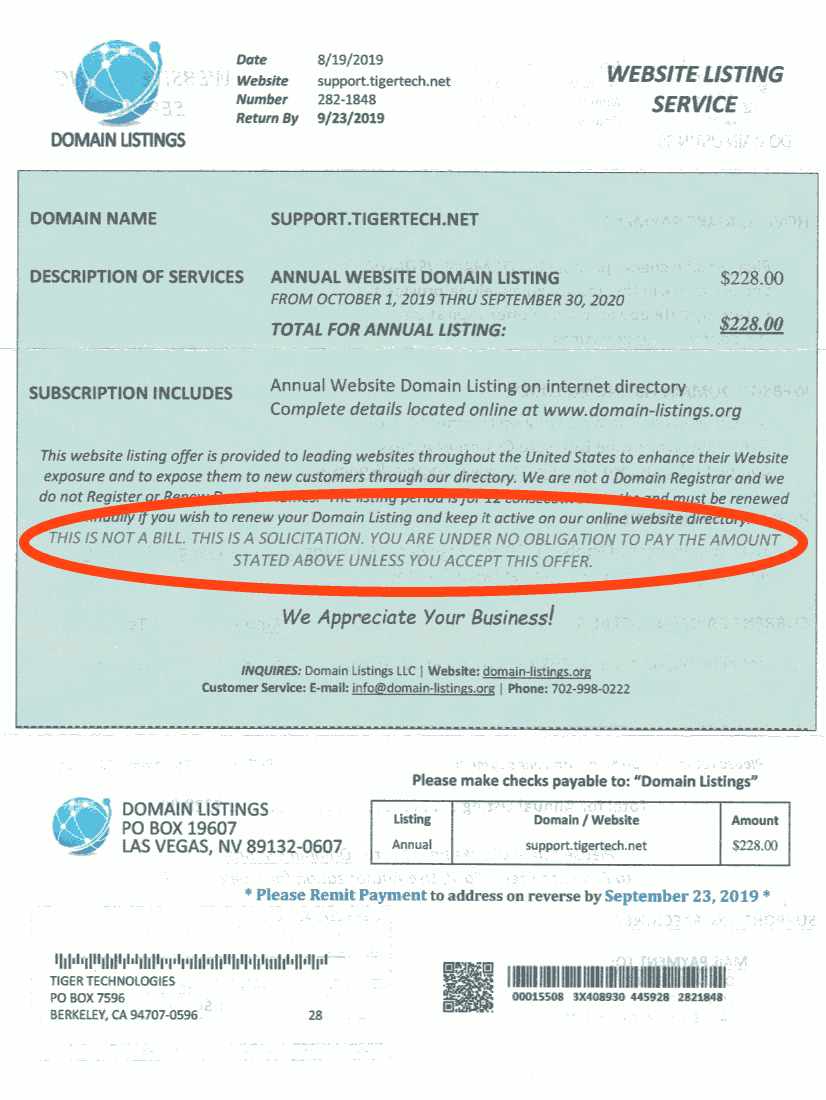
If you’re using an old version of a mail program that shows an error, it may allow you to add an “exception” or check a box telling it to always trust the certificate anyway — it might look like this if you show the certificate details, for example:
If it doesn’t allow that, you can either disable SSL in the settings of that mail program (for example, by unchecking the “Use SSL” checkbox in older versions of Apple Mail), or you can use the Firefox web browser to read your mail using webmail. If you’re one of our customers, that’s at webmail.tigertech.net.
Read the rest of this entry »
We recently heard from a couple of customers who set up Gmail to “Send mail as” a different email address at their custom domain name many years ago, and who are now having problems sending mail to people who use Outlook.com for their mail service (the messages were wrongly being flagged as spam at Outlook).
If this happens to you, it’s because the way Gmail used to set this up doesn’t interact well with modern email providers. The way they send these messages makes it look like a “spam forgery” to providers like Outlook.com that check for DKIM and SPF.
You can easily solve this by deleting the address in Gmail, then re-adding it. (If you’re one of our customers, the “Using Gmail to send messages” section of this page on our website shows the settings to use at Gmail.) Google will then set it up in a better way that works with modern email providers.
Read the rest of this entry »
We’ve seen a few reports recently of customers receiving messages that begin something like this:
I’m going to cut to the chase. I am aware [redacted] is your pass word. More to the point, I know your secret and I’ve evidence of your secret. You don’t know me personally and no one paid me to examine you.
Or like this:
You may not know me and you are probably wondering why you are getting this e mail, right? I’m a hacker who cracked your email and devices a few months ago. Do not try to contact me or find me, it is impossible, since I sent you an email from YOUR hacked account.
The message then goes on to demand money (usually in the form of a Bitcoin ransom) in order to not reveal your “secret”.
These are a scam; you should ignore them. The mail is sent in bulk by spammers to millions of people, just like any other spam, and they know nothing about you beyond your email address and possibly a password they stole from another site. Our filters block most of these (we’re blocking more than a dozen per day per account, on average), but unfortunately no filter can block all spam messages, and the spammers are constantly changing them to get around the blocking.
You can find more information on sites like Sophos and Krebs on Security.
Read the rest of this entry »
We’ve had reports of an error message like this in Outlook when using Windows 10:
error (0x800CCC13): Cannot connect to the network. Verify your network connection or modem.
If this happens to you, it’s because of a problem with Windows 10, not with Outlook or our servers. According to the Microsoft page about it, updating Windows 10 should fix it. If it doesn’t, they suggest using a “workaround” to repair corrupted files on your computer.
The PHP developers recently released PHP version 7.0.0, as well as an update to the 5.6 series, version 5.6.16. We’ve upgraded PHP on our servers as a result.
The official release of PHP 7 means we’ll start encouraging customers to use it (as long as they use modern scripts like current versions of WordPress). It’s almost twice as fast as old versions of PHP. Yes, really: Twice as fast. We’re using it ourselves on this blog.
If you’d like your WordPress or other PHP-based site to seem snappier, or be able to handle twice as many visitors per second, you can easily do so:
- Login to our My Account control panel
- Click PHP Settings
- Click PHP 7.0 series
- Click Save Settings
Then test your site to make sure it works properly. If it does: Great, you’ve just made your site much faster! If it doesn’t, it’s probably because you’re using older scripts that haven’t yet been updated, and you can simply set PHP back to an earlier version for now. We recommend that you always use the latest version that works properly with your scripts.
As always, if you have any trouble, don’t hesitate to contact us.
If you use an SSL certificate on a site you host with us, we now offer more control over the SSL/TLS protocol versions your site uses.
Old protocol versions, including SSL version 3 (“SSLv3”) and TLS version 1.0, are no longer considered secure. You can now disable these to improve security, at the expense of preventing some older, less-secure browsers from making SSL or TLS connections. Some credit card companies are starting to require that SSLv3 and TLS 1.0 both be disabled.
Read the rest of this entry »
If you use WordPress blog software on your site, be sure to upgrade to WordPress 3.0.2 as soon as possible. The upgrade contains an important security fix for a vulnerability that allows any WordPress “author” to become an “administrator”.
Although all WordPress users should upgrade right away, we’ve added security rules to our servers to protect our Web hosting customers who haven’t yet upgraded. Other people may find the rules useful if they use mod_security on Apache Web servers. The rest of this post contains more technical details.
Read the rest of this entry »